Get complete visibility & uncover exposures in minutes with runZero — no agents, credentials, or appliances required.
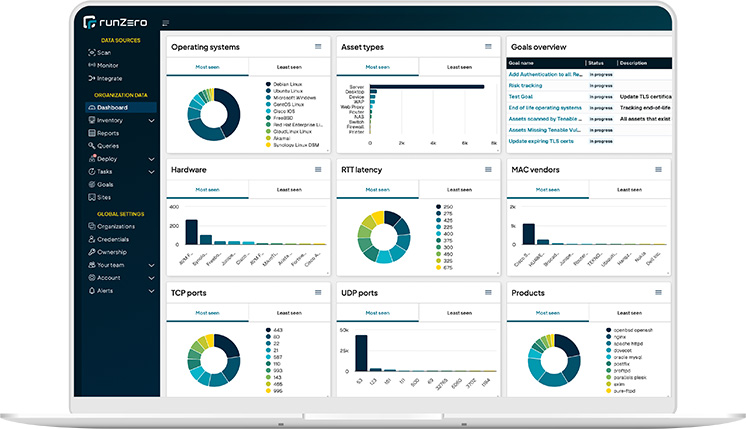
runZero delivers the fastest, most complete security visibility possible across your assets and internal and external attack surfaces, so you can mitigate exposures before they can be compromised — and stay compliant.
The runZero Platform is the only CAASM (cyber asset attack surface management) solution that combines powerful proprietary active scanning, native passive discovery, and API integrations. Unifying these discovery approaches makes our platform unique in its ability to discover and provide accurate, detailed fingerprinting for all IT, OT, and IoT devices across on-prem, cloud, and remote environments.